The payment card industry data security standards, commonly referred to as PCI DSS, are the globally recognized framework of security controls that any organization storing, processing, or transmitting cardholder data must implement and maintain. As of March 31, 2024, PCI DSS version 4.0.1 became the mandatory standard, replacing the older 3.2.1 framework with updated technical and operational requirements designed to address the evolving threat environment. For government agencies processing license fees, utility payments, permit applications, and other public-facing transactions, meeting the payment card industry data security standards is both a regulatory obligation and a public trust responsibility. This checklist walks through the specific controls, audit requirements, and compliance review processes that agencies need to have in place to demonstrate and sustain PCI DSS compliance.
Key Takeaways
- PCI DSS 4.0.1 is now mandatory for all cardholder data environments: Government agencies processing any card-based payment, including online portals, in-person kiosks, and phone payments, must align their infrastructure and procedures with the updated payment card industry data security standards.
- Only 27.9% of organizations are fully PCI DSS compliant, according to Verizon’s Payment Security Report: The majority of organizations that experience breaches are found to have been non-compliant at the time of the incident, making a structured compliance checklist essential rather than optional.
- Non-compliance with the payment card industry data security standards carries direct financial consequences: Fines from card brands and acquiring banks can reach $100,000 per month, and breach-related costs, including forensic investigations and customer remediation, can exceed $500,000 per incident.
Public Sector Controls for Payment Card Industry Data Security Standards
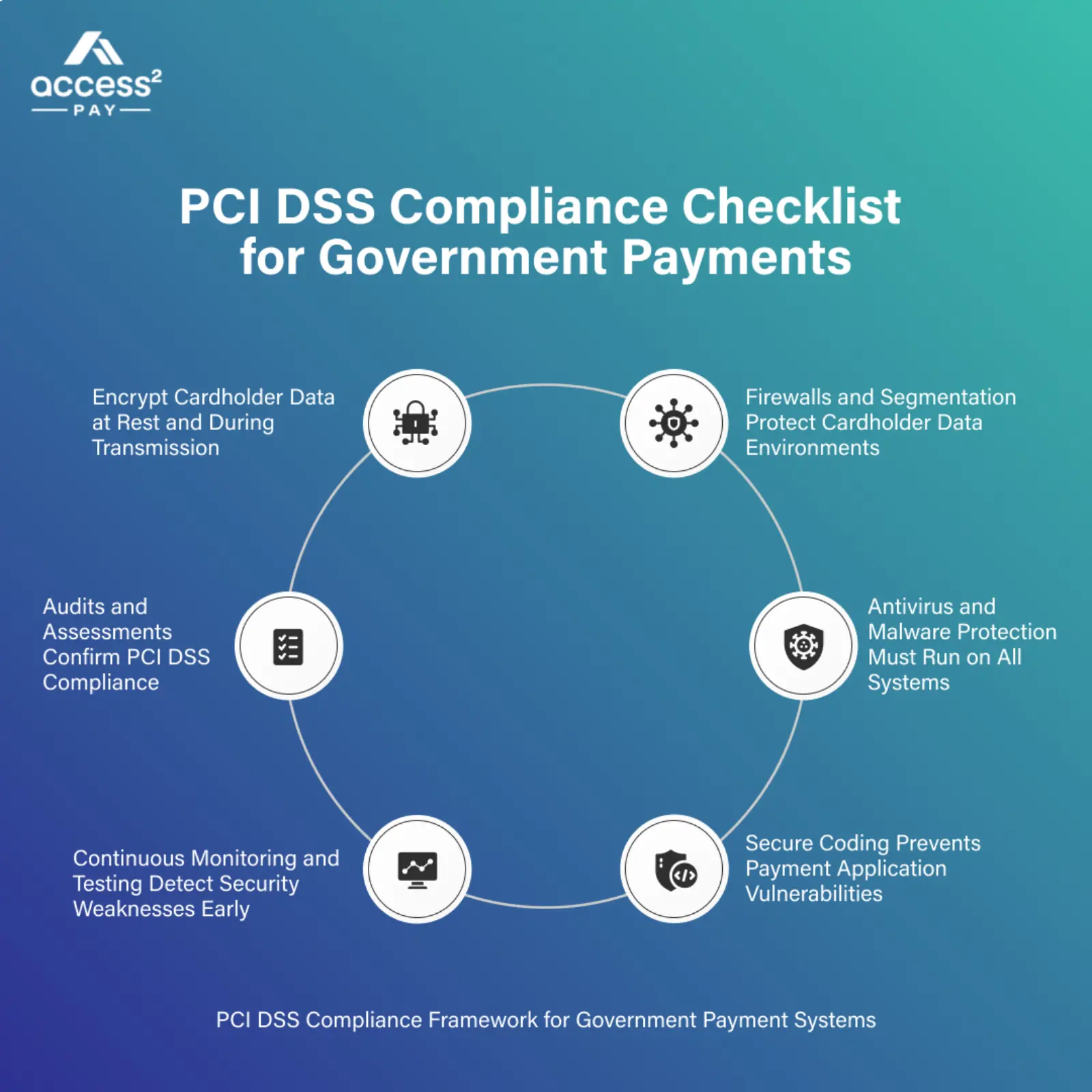
Public sector organizations face specific implementation challenges in meeting the payment card industry data security standards because their payment environments often span multiple departments, legacy systems, and citizen-facing channels that were not originally designed with PCI DSS in mind. Agencies using a purpose-built platform such as Access2Pay’s government payment solution begin from a compliant infrastructure baseline, which significantly reduces the scope of the technical controls they need to implement and maintain independently. The six control areas below form the foundation of any public sector compliance posture under the Payment Card Industry Data Security Standards.
Encryption Protocols in Payment Card Industry Data Security Standards
Encryption is the primary technical control for protecting cardholder data both while it is stored and while it is transmitted across networks. The payment card industry data security standards require strong cryptography for all cardholder data at rest and mandate TLS 1.2 or higher for all data in transit, with any earlier versions of SSL and TLS explicitly prohibited.
- End-to-end encryption for all card data in transit: Every path through which cardholder data travels, between a citizen’s browser and the payment portal, between the portal and the payment processor, or between internal systems, must use current TLS encryption standards with no fallback to deprecated protocols.
- Encryption key management procedures: The payment card industry data security standards require documented procedures for generating, storing, distributing, retiring, and destroying encryption keys, with key custodian roles assigned to specific individuals and key access restricted accordingly.
- Data at rest protection for stored cardholder data: Where the payment card industry data security standards permit any storage of primary account numbers, that stored data must be rendered unreadable through strong one-way hashing, truncation, tokenization, or encryption with appropriate key management controls.
Firewall Configurations Supporting Payment Card Industry Data Security Standards
Firewall configuration is one of the first and most foundational requirements of the payment card industry data security standards, covering both the network perimeter and the internal boundaries between the cardholder data environment and all other network segments. A correctly configured firewall ruleset restricts inbound and outbound traffic to only what is explicitly required for business operations, denying everything else by default.
- Documented and approved firewall ruleset: Every firewall rule permitting traffic into or out of the cardholder data environment must be individually justified, documented, and reviewed at least every six months under the Payment Card Industry Data Security Standards (PCI DSS).
- Network segmentation between CDE and other systems: Systems that do not need to communicate with cardholder data must be isolated from the cardholder data environment by firewall controls, reducing the scope of systems that fall under payment card industry data security standards compliance requirements.
- Default-deny inbound and outbound traffic rules: Firewall configurations must deny all traffic not explicitly permitted, and all outbound connections from the cardholder data environment must be specifically authorized rather than open by default.
Antivirus and Malware Protection per Payment Card Industry Data Security Standards
The payment card industry data security standards require that all systems commonly affected by malware have antivirus software deployed, kept current, and configured to generate audit logs. For government agencies, this requirement extends to workstations, servers, and point-of-sale terminals, with particular attention to any device that processes or has access to cardholder data.
- Antivirus deployment on all applicable systems: Antivirus and anti-malware software must be installed on all systems within the scope of the payment card industry data security standards, with automatic definition updates configured and verified on a schedule that does not leave systems exposed to emerging threats.
- Real-time malware detection and alerting: Antivirus software must be configured to run in active protection mode, detecting and alerting on malicious activity in real time rather than relying on scheduled scans alone, which would leave a window of exposure between scan cycles.
- Anti-malware audit log generation: Antivirus activity logs must be enabled and retained in accordance with the Payment Card Industry Data Security Standards log retention requirements, providing an auditable record of malware detection events and response actions for each in-scope system.
Secure Application Development Following Payment Card Industry Data Security Standards
The payment card industry data security standards require that all software applications used to process cardholder data be developed according to secure coding practices, with change management controls, code review procedures, and vulnerability testing built into the development lifecycle. According to IBM’s Cost of a Data Breach Report 2024, the global average cost of a data breach reached $4.88 million in 2024, a figure that reinforces the financial case for embedding payment card industry data security standards controls into application development before deployment rather than remediating vulnerabilities discovered after a breach.
- Secure coding standards and developer training: All developers working on applications that interact with cardholder data must be trained in secure coding practices relevant to their programming language and framework, with training updated at least annually under the payment card industry data security standards.
- Code review and testing before production deployment: All application changes that could affect the cardholder data environment must undergo code review and security testing before deployment to production, with the results documented and retained as part of the compliance record.
- Web application firewall for public-facing applications: Public-facing web applications that interact with cardholder data must be protected by either a web application firewall configured to detect and block common attacks or an application vulnerability assessment process conducted at least annually.
Physical Access Restrictions for Payment Card Industry Data Security Standards
Physical access controls under the Payment Card Industry Data Security Standards require that the systems, servers, and network components within the cardholder data environment be physically secured against unauthorized access. For government agencies, this applies to server rooms, network closets, payment kiosk hardware, and any workstation where cardholder data is processed.
- Facility entry controls for cardholder data areas: Access to areas containing payment card industry data security standards in-scope systems must be restricted to authorized personnel, with access controlled by badge readers, PIN entry, or other mechanisms that produce an auditable entry log.
- Physical media handling and disposal procedures: Any physical media containing cardholder data, including printed reports, backup drives, and decommissioned hardware, must be destroyed through documented procedures that render the cardholder data unrecoverable before disposal.
- Visitor management and escort requirements: Visitors to areas containing cardholder data environment components must be authorized, logged, and escorted by an authorized staff member, with visitor badges visually distinguishable from employee credentials.
Transmission Security for Payment Card Industry Data Security Standards
Transmission security under the payment card industry data security standards covers all paths through which cardholder data moves between systems, including internal network transmission, external connections to payment processors, and any wireless networks used in payment environments.
- TLS 1.2 or higher for all cardholder data transmission: No cardholder data may be transmitted over a public network without strong cryptographic protection, and the specific versions of TLS used must be current and compliant with the payment card industry data security standards cryptographic requirements.
- Wireless network isolation and security configuration: Any wireless network that could provide access to the cardholder data environment must use strong encryption, change default vendor credentials, and be logically isolated from the broader network with documented firewall rules controlling the boundary.
- No cardholder data via unprotected messaging: Cardholder data must never be transmitted through end-user messaging technologies such as email, instant messaging, or SMS without strong encryption, and documented policies must explicitly prohibit unprotected transmission regardless of internal convenience.
Audits and Testing Under Payment Card Industry Data Security Standards
Ongoing testing and auditing requirements are one of the most operationally demanding aspects of the payment card industry data security standards, because they are not annual events but recurring obligations distributed throughout the calendar year. Organizations that treat PCI DSS testing as a once-per-year project rather than a continuous program routinely find themselves non-compliant between assessment cycles. The Verizon Payment Security Report has consistently found that organizations are less compliant in the months following their annual assessment than at the point of assessment itself, highlighting the importance of building testing into regular operations rather than treating it as a compliance milestone.
Quarterly Network Scans for Payment Card Industry Data Security Standards
The payment card industry data security standards require quarterly external vulnerability scans of all internet-facing systems in the cardholder data environment, conducted by a PCI SSC-approved scanning vendor. Internal vulnerability scans must also be conducted quarterly and after any significant network change.
- Approved scanning vendor engagement: External quarterly scans must be conducted by a vendor on the PCI SSC’s approved scanning vendor list, not by the organization’s own security team, and the resulting scan report must demonstrate that no high-severity vulnerabilities were detected or that detected vulnerabilities were remediated.
- Internal scan scope and frequency: Internal network scans covering all in-scope systems must be conducted quarterly and repeated after any significant change to the cardholder data environment, with scan results retained as documentation of continuous compliance with the payment card industry data security standards.
- Remediation and rescan requirements: Any vulnerability identified in a quarterly scan that meets the payment card industry data security standards threshold for remediation must be addressed within the timeframe specified by the standard, followed by a rescan confirming that the vulnerability is resolved before the scan period closes.
Penetration Testing Schedules in Payment Card Industry Data Security Standards
Penetration testing under the Payment Card Industry Data Security Standards requires at least annual testing of the external network perimeter, internal network segmentation controls, and application layer of the cardholder data environment, with additional testing required after any significant infrastructure or application change.
- Annual external and internal penetration testing: A qualified penetration tester must attempt to exploit vulnerabilities in both the external perimeter and the internal network of the cardholder data environment at least annually, with the scope, methodology, and results documented and retained as a compliance record.
- Segmentation control validation: If an organization relies on network segmentation to reduce the scope of its payment card industry data security standards compliance obligations, annual penetration testing must explicitly verify that segmentation controls are effective and that out-of-scope systems cannot reach cardholder data environment systems.
- Post-significant-change testing requirement: Any significant change to the cardholder data environment, such as a new payment application, a network redesign, or a cloud migration, must trigger penetration testing before the changed environment processes live cardholder data.
Intrusion Detection Reviews per Payment Card Industry Data Security Standards
Intrusion detection systems monitor network traffic and system behavior for signs of unauthorized access or malicious activity within the cardholder data environment. The payment card industry data security standards require that these systems be deployed, that alerts be reviewed daily, and that the systems be tested to confirm they are functioning as intended.
- IDS or IPS deployment at cardholder data environment boundaries: Intrusion detection or prevention systems must be positioned at all points where traffic enters or leaves the cardholder data environment, with rulesets maintained and updated to detect current attack patterns.
- Daily review of IDS alerts and logs: Security personnel must review intrusion detection alerts and logs at least daily under the Payment Card Industry Data Security Standards, with documented procedures for escalating and investigating any alert that cannot be immediately classified as a known false positive.
- IDS effectiveness testing: The intrusion detection system must be tested periodically to confirm that it is generating alerts correctly, using known-safe test signatures, so that teams can confirm the system would detect actual intrusion attempts.
Rogue Software Detection Tools for Payment Card Industry Data Security Standards
The payment card industry data security standards require that organizations deploy file integrity monitoring or change detection software on critical system files, configuration files, and content files, alerting administrators when unauthorized changes are detected.
- File integrity monitoring on critical files: File integrity monitoring must cover operating system files, application executables, configuration files, and content files for all in-scope systems, with a baseline established at installation and alerts generated for any deviation from that baseline.
- Alert response procedures for unauthorized changes: When file integrity monitoring detects an unauthorized change in the cardholder data environment, documented response procedures must direct the reviewing team through investigation, containment, and remediation steps with defined timelines.
- Scheduled integrity check intervals: File integrity checks must be performed at intervals sufficient to detect unauthorized changes before they can be exploited, with the frequency informed by the sensitivity of the affected system and the threat profile of the cardholder data environment.
Security Awareness Training Meeting Payment Card Industry Data Security Standards
Security awareness training is a specific requirement of the payment card industry data security standards, not a general best practice. All personnel with access to cardholder data must receive security awareness training upon hire and at least annually thereafter, with the training program updated to address current threats.
- Annual training completion for all in-scope personnel: Every employee, contractor, or vendor staff member with access to cardholder data or cardholder data environment systems must complete documented security awareness training at least once per year, with completion records retained for compliance review.
- Phishing and social engineering awareness components: Training programs must address the specific social engineering and phishing tactics that target payment data, because human factors remain a leading cause of payment card industry data security standards violations even in technically well-controlled environments.
- Training content updates for emerging threats: Security awareness training content must be reviewed and updated annually to reflect changes in the threat landscape and in the organization’s own payment environment, ensuring staff remain prepared for current attack vectors.
Incident Response Testing for Payment Card Industry Data Security Standards
The payment card industry data security standards require organizations to have a documented incident response plan that specifically addresses cardholder data breaches, with the plan tested at least annually and updated based on lessons learned. According to a 2024 report by Accutive Security, public sector organizations face average breach costs of $2.99 million, a figure that demonstrates the direct financial relevance of having a tested, functional incident response capability specifically for cardholder data incidents.
- Documented incident response plan covering cardholder data breaches: The incident response plan must specifically address the steps for containing a breach of the cardholder data environment, notifying card brands and acquiring banks within required timeframes, and managing the forensic investigation process.
- Annual tabletop or simulated breach exercise: The incident response plan must be tested at least annually through a tabletop exercise or simulated incident, with participants from all departments that would be involved in a real breach response, and the exercise findings documented and used to update the plan.
- Post-incident review and plan update: After any security incident affecting or potentially affecting the cardholder data environment, the incident response plan must be reviewed and updated to incorporate lessons learned before the next annual review cycle.
Compliance Reviews for Payment Card Industry Data Security Standards
Compliance reviews under the payment card industry data security standards are the formal processes through which an organization validates, documents, and reports its compliance status to the card brands, acquiring banks, and regulatory bodies that require it. These reviews range from self-assessment questionnaires for lower-volume merchants to formal reports on compliance from a qualified security assessor for the highest transaction-volume organizations. Access2Pay’s provincial payment platform supports agencies in managing compliance documentation and reporting requirements through a platform that is itself built to PCI DSS standards, reducing the compliance scope that government agencies must demonstrate independently.
Self-Assessment Questionnaires for Payment Card Industry Data Security Standards
Self-assessment questionnaires are structured compliance review tools published by the PCI SSC that allow eligible organizations to assess and document their own adherence to the payment card industry data security standards without requiring an on-site assessment by a qualified security assessor.
- SAQ type selection based on payment environment: Different SAQ types apply to different payment acceptance methods; government agencies must correctly identify which SAQ applies to each component of their payment environment, since using an incorrect SAQ type can result in an invalid compliance declaration.
- Annual completion and attestation requirement: Eligible organizations must complete and sign the appropriate self-assessment questionnaire annually, with the attestation of compliance submitted to their acquiring bank by the required deadline to maintain payment processing privileges.
- SAQ completion accuracy and evidence retention: Each SAQ response must reflect the actual state of the relevant control, supported by documented evidence, because an inaccurate self-assessment that overstates compliance does not protect the organization from penalties if a breach subsequently reveals the true compliance status.
Report on Compliance Documentation Under Payment Card Industry Data Security Standards
Organizations at Level 1 merchant status, processing over six million card transactions per year, are required to obtain an annual Report on Compliance from a PCI SSC-qualified security assessor rather than completing a self-assessment questionnaire. The report on compliance documents the assessor’s findings across all twelve payment card industry data security standards requirements.
- Qualified security assessor engagement: A Level 1 merchant or service provider must engage a QSA from the PCI SSC’s approved QSA company list to conduct the annual on-site assessment, with the scope of the assessment covering all systems, processes, and people within the cardholder data environment.
- Report on compliance structure and required sections: The report on compliance must follow the PCI SSC’s defined format, covering all twelve payment card industry data security standards requirements with the assessor’s findings, evidence references, and compensating controls documented for each applicable control.
- Report submission and retention timelines: Completed reports on compliance must be submitted to the acquiring bank and card brands within the timelines they specify, and the organization must retain the full report and supporting evidence for the period required by the payment card industry data security standards and applicable regulatory requirements.
Third-Party Service Provider Reviews for Payment Card Industry Data Security Standards
The payment card industry data security standards hold organizations accountable for the compliance status of the third-party service providers they engage to process, store, or transmit cardholder data. An organization cannot outsource its PCI DSS obligation; it must verify that every relevant third party meets the same standards.
- Annual confirmation of third-party PCI DSS compliance: Organizations must maintain a list of all third-party service providers with access to cardholder data and confirm at least annually that each provider is PCI DSS compliant, either through a current AOC or through independent verification.
- Contractual compliance requirements for service providers: Contracts with third-party service providers that interact with cardholder data must include explicit requirements for payment card industry data security standards compliance and the right to audit the provider’s compliance status.
- Monitoring for changes in third-party compliance status: Organizations must actively monitor for any communication from a third-party provider indicating a change in compliance status or a breach of their payment environment, and have procedures for responding to such changes without disruption to their own compliance posture.
Remediation Tracking in Payment Card Industry Data Security Standards Audits
Remediation tracking is the structured process of recording, assigning, and following up on every gap or finding identified during a payment card industry data security standards assessment or ongoing monitoring review. Without disciplined tracking, identified vulnerabilities remain open, and the organization’s compliance posture degrades between formal assessments.
- Centralized remediation register for all PCI DSS findings: Every finding from any assessment, scan, penetration test, or monitoring alert must be entered into a centralized tracking register with the finding description, severity, assigned owner, remediation steps, and target resolution date.
- Escalation procedures for overdue remediations: Remediation items that approach or pass their target date without resolution must trigger an escalation to senior management, ensuring that payment card industry data security standards compliance gaps receive appropriate organizational priority.
- Evidence capture at remediation completion: When a remediation item is closed, the resolution must be documented with supporting evidence, such as configuration screenshots, test results, or training records, so that the closure can be substantiated during the next assessment.
Annual Validation Processes for Payment Card Industry Data Security Standards
Annual validation pulls together the full body of evidence generated throughout the year, including scan results, penetration test reports, training records, policy reviews, and configuration documentation, into a coherent compliance demonstration that supports the SAQ attestation or report on compliance submission.
- Compliance evidence collection schedule: Organizations should maintain a running evidence collection process throughout the year rather than scrambling to gather documentation at assessment time, using a documented schedule that assigns evidence collection responsibilities to specific roles.
- Policy and procedure review cycle: All policies and procedures relevant to the payment card industry data security standards, including information security policy, acceptable use policy, and incident response plan, must be reviewed at least annually and updated to reflect any changes in the operating environment or the standard itself.
- Executive sign-off on annual compliance attestation: The annual attestation of compliance under the payment card industry data security standards must be signed by a senior officer of the organization, confirming that the SAQ or ROC accurately represents the organization’s compliance status for the assessment period.
Continuous Monitoring Dashboards for Payment Card Industry Data Security Standards
Continuous monitoring dashboards aggregate real-time data from network scanning, log management, file integrity monitoring, and vulnerability management tools into a single operational view, enabling security teams to identify compliance drift as it occurs rather than at the point of annual assessment.
- Centralized log management and SIEM integration: All systems within the cardholder data environment must generate logs that feed into a centralized security information and event management system, providing the aggregated, time-correlated view of activity that the payment card industry data security standards require for effective monitoring.
- Compliance metric tracking and trend reporting: Dashboards should track key compliance metrics over time, such as the number of open vulnerabilities, the age of unresolved exceptions, and the currency of antivirus definitions, providing trend data that allows teams to identify compliance degradation before it reaches a reportable threshold.
- Alerting thresholds aligned to payment card industry data security standards requirements: Monitoring alerts must be configured to reflect the specific detection and response timeframes required by the payment card industry data security standards, so that teams are notified in time to respond within the compliance-mandated windows.
Frequently Asked Questions
What is the difference between PCI DSS 3.2.1 and PCI DSS 4.0.1?
PCI DSS 4.0.1 replaced version 3.2.1 as the mandatory standard on March 31, 2024, introducing updated requirements that address modern attack vectors, offer greater flexibility in how controls are implemented, and shift the philosophy of the payment card industry data security standards from point-in-time compliance toward a continuous security posture. Key changes include more rigorous authentication requirements, expanded multi-factor authentication scope, new requirements for phishing-resistant authentication methods, and additional customized implementation options that allow organizations to demonstrate an equivalent level of protection through compensating controls. Organizations that were assessed against 3.2.1 prior to that date must now complete their next validation cycle under 4.0.1, and the PCI SSC has published transition resources to help organizations identify the specific gaps between their existing compliance program and the updated requirements.
Does using a third-party payment processor remove my organization from PCI DSS scope?
Using a third-party processor reduces the scope of the payment card industry data security standards requirements your organization must meet independently, but it does not eliminate your compliance obligations entirely. If your organization’s systems ever transmit, process, or store cardholder data, even briefly, those systems remain in scope, and your organization must verify and document the third-party processor’s own compliance status at least annually. Platforms such as Access2Pay’s government payment solution are built to PCI DSS standards and provide an attestation of compliance that government agencies can use to demonstrate vendor compliance as part of their own compliance program, significantly simplifying the third-party review obligation.
What are the consequences of failing a PCI DSS assessment for a government agency?
A government agency that fails a payment card industry data security standards assessment faces several immediate consequences: the acquiring bank may impose monthly non-compliance fees ranging from $5,000 to $100,000 until compliance is restored, payment card processing privileges may be restricted, and a mandatory remediation plan with specific timelines must be agreed upon and tracked. If a data breach occurs during a period of non-compliance, additional consequences include forensic investigation costs, card reissuance fees of up to $90 per compromised record, and reputational damage that can undermine public confidence in the agency’s ability to handle citizen financial data. The Security Journey compliance research estimates total breach remediation costs at between a few thousand dollars and $500,000 depending on breach scope, a range that in every scenario significantly exceeds the cost of maintaining a compliant program from the outset.
Implementing Payment Card Industry Data Security Standards For Business Security
Achieving and maintaining compliance with the payment card industry data security standards is an ongoing operational discipline, not a one-time project. The checklist covered in this article spans three operational dimensions: the technical controls that protect cardholder data at the infrastructure level, the testing and auditing processes that verify those controls are functioning as intended, and the compliance review procedures that document and report the organization’s compliance status to the parties that require it. Each dimension depends on the others, because a technically sound environment with weak audit procedures will fail at assessment time, and strong documentation without effective technical controls is simply an accurate record of insufficient protection.
For government agencies specifically, the payment card industry data security standards represent a foundational layer of the trust that citizens place in public institutions when they submit card payments for taxes, licenses, permits, and services. Deploying a payment infrastructure that is built for compliance from the ground up is the most efficient path to meeting those obligations. Access2Pay’s government payment platform offers PCI DSS-compliant processing for municipal agencies and provincial and state governments, providing the technical foundation that agencies need to reduce compliance scope, simplify their audit process, and demonstrate to their constituents and oversight bodies that payment card data is handled with the security it requires.
Sources
-
- IBM Security. (2024). Cost of a data breach report 2024. Cited in: Accutive Security.
https://accutivesecurity.com/data-breach-statistics-2024-penalties-and-fines-for-major-regulations/ - PCI Security Standards Council. (2024). PCI DSS v4.0.1 resource hub.
https://www.pcisecuritystandards.org/ - IBM Security. (2024). Cost of a data breach report 2024. Cited in: Datatel Systems.
https://www.datatel-systems.com/article/ibm-report-data-breaches-2024/ - Verizon. (2023). Payment security report. Cited in: GoAnywhere MFT.
https://www.goanywhere.com/blog/the-5-biggest-pci-compliance-breaches - Accutive Security. (2024). Data breach statistics 2024: Penalties and fines for major regulations.
https://accutivesecurity.com/data-breach-statistics-2024-penalties-and-fines-for-major-regulations/ - Comforte. (2024, May 16). Counting the cost of PCI DSS non-compliance.
https://insights.comforte.com/counting-the-cost-of-pci-dss-non-compliance - Security Journey. (2024). The true cost of PCI-DSS non-compliance.
https://www.securityjourney.com/post/the-true-cost-of-pci-dss-non-compliance - Clone Systems. (2024). The true cost of PCI DSS 4.0.1 non-compliance: Fines, risks, and what you need to know.
https://www.clone-systems.com/the-true-cost-of-pci-dss-4-0-1-non-compliance-fines-risks-and-what-you-need-to-know/ - Access2Pay. (2025). Government payment solutions.
https://access2pay.com/government-payments/ - Access2Pay. (2025). Municipal government payments.
https://access2pay.com/government-payments/municipal-government/ - Access2Pay. (2025). Provincial and state government payment solutions.
https://access2pay.com/government-payments/provincial-and-state-government/
- IBM Security. (2024). Cost of a data breach report 2024. Cited in: Accutive Security.